CVE-2024-57030: Cross-Site Scripting (XSS) Stored in documentos_funcionario.php parameter id
CVE Publication: https://www.cve.org/CVERecord?id=CVE-2024-57030
Vendor
WeGIA (Web Gerenciador Institucional) is an integrated management system licensed under the GNU GPL v3.0, designed to enhance administration, control, and transparency for institutions.
https://sol.sbc.org.br/index.php/latinoware/article/view/31544
Affected Product Code Base
WeGIA < v3.2.0
Vulnerability Description
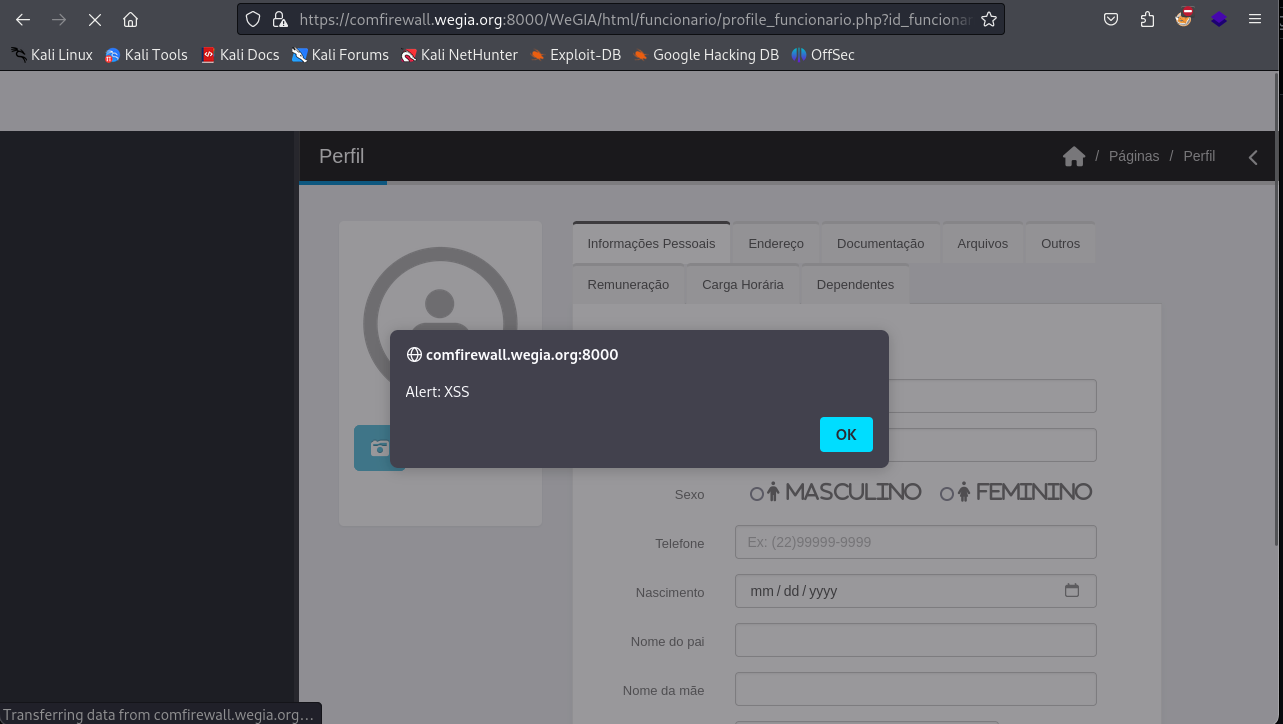
A stored Cross-Site Scripting (XSS) vulnerability was identified in the WeGIA application. This vulnerability allows unauthorized scripts to be executed within the user's browser context. Stored XSS is particularly critical, as the malicious code is permanently stored on the server and executed whenever a compromised page is loaded, affecting all users accessing this page.
POC
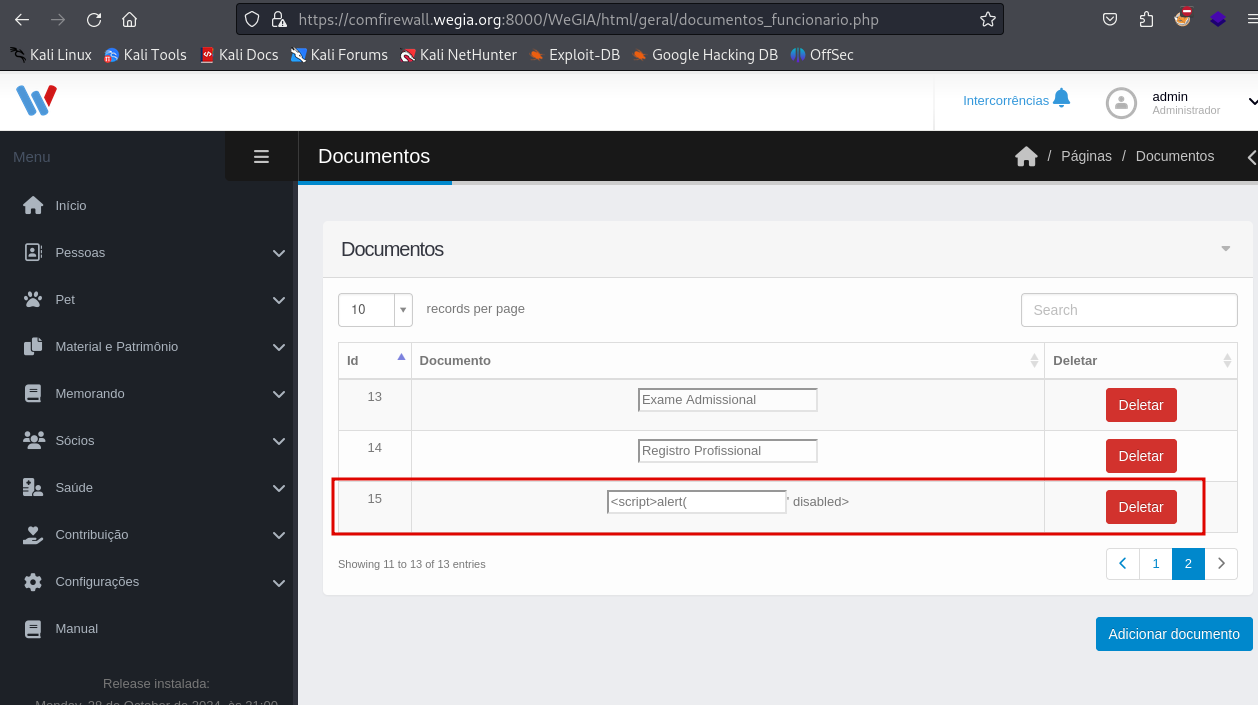
To reproduce the issue, insert the following payloads into the vulnerable field of the URL and save the changes:
| |
After saving the input, the injected script will be stored on the server and automatically executed for any user accessing the html/geral/documentos_funcionario.php, confirming the stored XSS.
File: documentos_funcionario.php
Payload:
| |
Trigger in: html/geral/documentos_funcionario.php
Endpoint: id
References
https://github.com/nilsonLazarin/WeGIA/issues/815
https://github.com/nilsonmori/WeGIA
Discoverer
By: CVE-Hunters

