CVE-2025-65014: Weak Password Policy Vulnerability in User Management Functionality
CVE Publication: https://www.cve.org/CVERecord?id=CVE-2025-65014
Summary
A Weak Password Policy vulnerability was identified in the user management functionality of the LibreNMS application. This vulnerability allows the creation of accounts with extremely weak and predictable passwords, such as 123456. This exposes the platform to brute-force and credential stuffing attacks.
Details
The application fails to enforce a strong password policy when creating new users. As a result, administrators can define trivial and well-known weak passwords, compromising the authentication security of the system.
Vulnerable Component: User creation / password definition
PoC
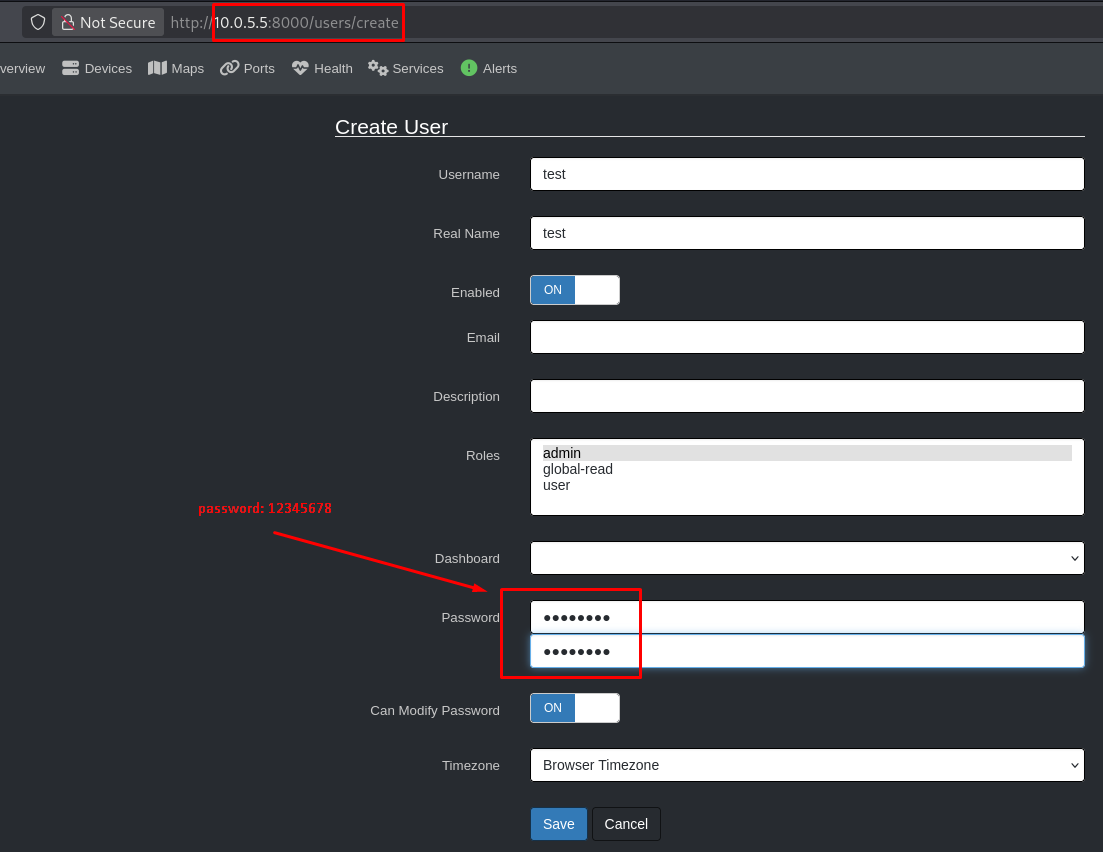
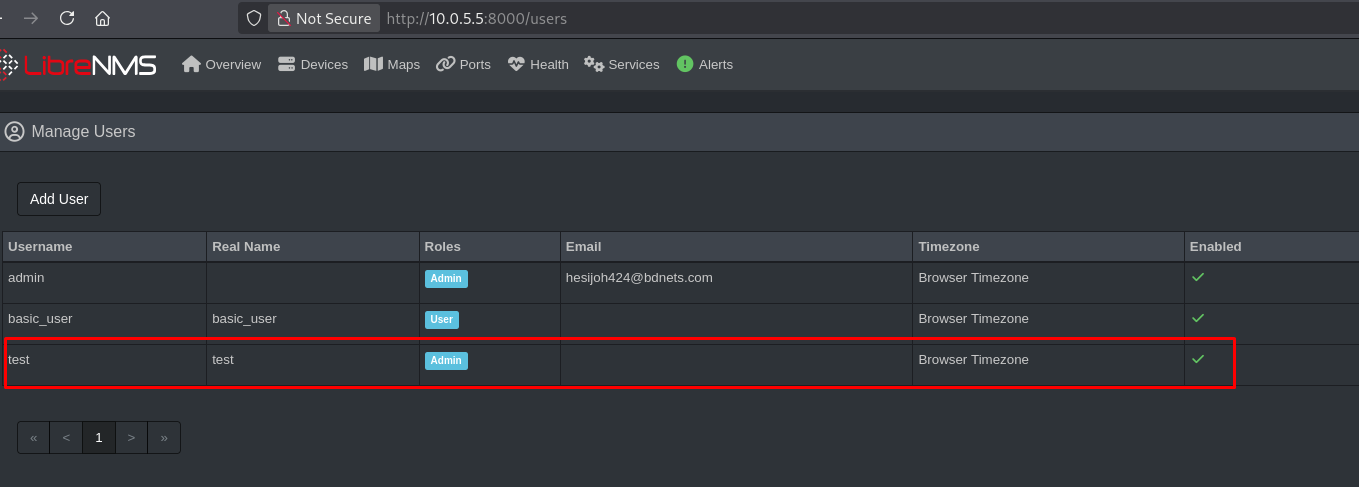
- Log in to the application using an Administrator account.
- Navigate to the user management section:
- Create a new user account using the password
12345678. - The application accepts the weak password without restrictions and creates the account successfully.
Impact
- Increased risk of brute-force and credential stuffing attacks.
- Unauthorized access to user or administrative accounts.
- Privilege escalation through compromised accounts.
- Reduced overall security posture of the application.
Reference
https://github.com/librenms/librenms/security/advisories/GHSA-5mrf-j8v6-f45g
Finder
By: CVE-Hunters

