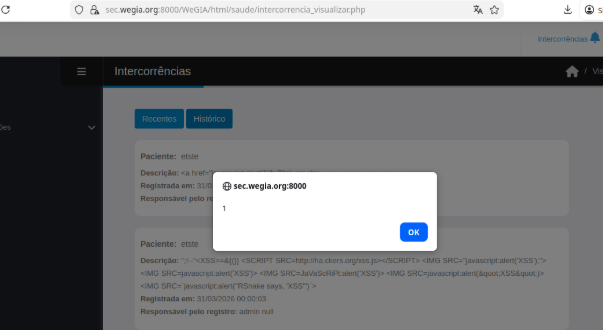
CVE-2026-40282: Cross-Site Scripting (XSS) Stored in intercorrencia_visualizar.php
CVE Publication: https://www.cve.org/CVERecord?id=CVE-2026-40282
Summary
A Stored Cross-Site Scripting (XSS) vulnerability allows an authenticated user to inject malicious JavaScript into the Intercorrências notification page, which is executed when user access the the page, enabling session hijacking and account takeover.
Details
The application does not properly sanitize or encode the user name field, which is displayed in system notifications and accepts user-controlled input. An attacker can inject malicious HTML or JavaScript into this field when creating or modifying a user.When an “intercorrência” is registered, a notification is generated. Upon clicking this notification, the application renders the user name in the interface without proper escaping, causing any injected code to be executed in the browser.This behavior demonstrates improper output encoding, resulting in a Stored XSS vulnerability.
- Vulnerable Endpoint:
intercorrencia_visualizar.php
PoC
Payload
| |
Steps to Reproduce:
1. Register a patient where the “Name” or "Sobrenome" field contains the payload.2. Add a "Intercorrência" entry for this user.3. Navigate to the "Intercorrências" notification page and click in "Recentes" and "Histórico. This vulnerability affects the both pages.4. Observe that the payload is executed in the browser:
Impact
- Session hijacking: Stealing cookies or authentication tokens to impersonate users.
- Credential theft: Harvesting usernames and passwords using malicious scripts.
- Malware delivery: Distributing unwanted or harmful code to victims.
- Privilege escalation: Compromising administrative users through persistent scripts.
- Data manipulation or defacement: Changing or disrupting site content.
- Reputation damage: Eroding trust among site users and administrators.
Reference
https://github.com/LabRedesCefetRJ/WeGIA/security/advisories/GHSA-r6h8-7vxv-q8pp
Finder
By: CVE-Hunters

