CVE-2026-40283: Cross-Site Scripting (XSS) Stored in profile_paciente.php
CVE Publication: https://www.cve.org/CVERecord?id=CVE-2026-40283
Summary
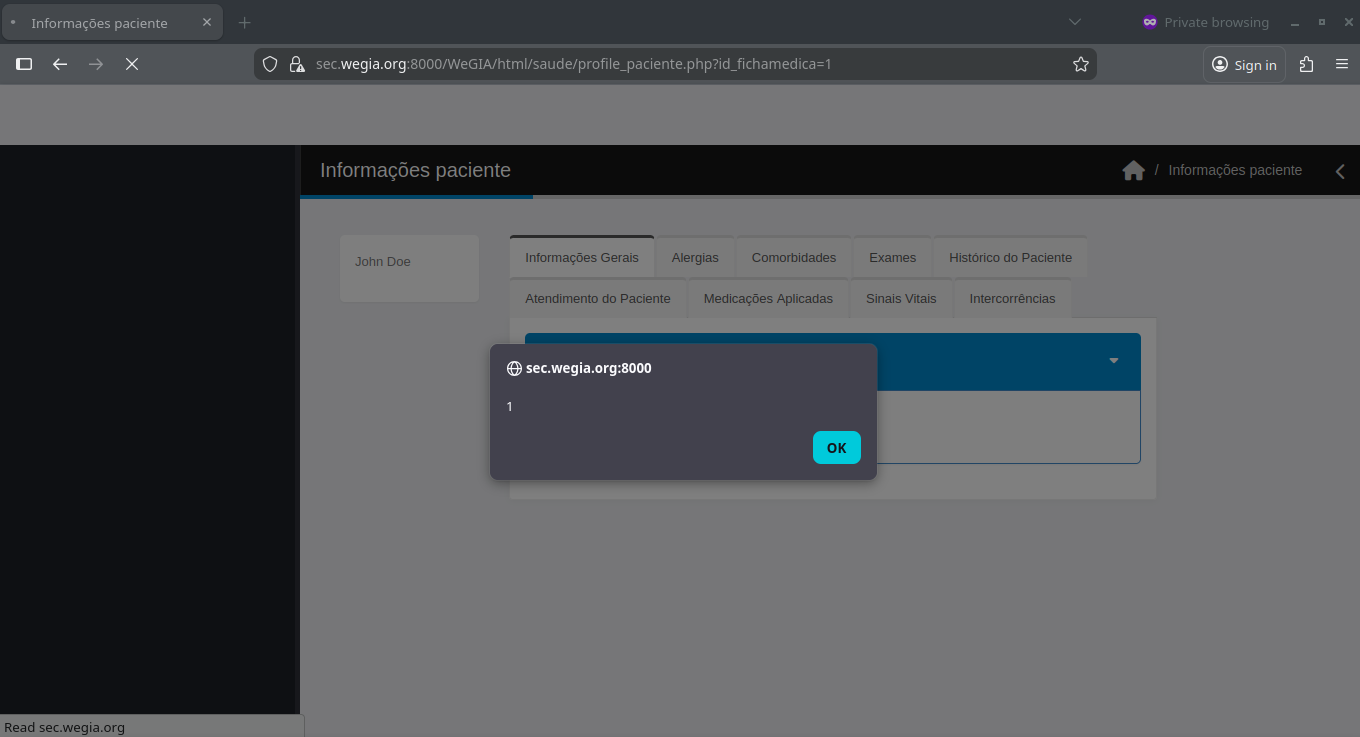
A Stored Cross-Site Scripting (XSS) vulnerability allows an authenticated user to inject malicious JavaScript via the “Nome” field in the “Informações Pacientes” page. The payload is stored and executed when the patient information is viewed.
Details
The application does not properly sanitize or encode the “Nome” field, which accepts user-controlled input. An attacker can insert malicious HTML or JavaScript into this field when creating or editing a patient.When the “Informações Pacientes” page is accessed, this value is rendered in the DOM without proper escaping, leading to execution of the injected code in the browser.This behavior indicates improper output encoding and results in a Stored XSS vulnerability.
- Vulnerable Endpoint:
profile_paciente.php
PoC
Payload
| |
Steps to Reproduce:
1. Register a patient where the “Name” field contains the payload.2. Navigate to the “Patient Information” page for the created patient.3. Observe that the payload is executed in the browser:
Impact
- Session hijacking: Stealing cookies or authentication tokens to impersonate users.
- Credential theft: Harvesting usernames and passwords using malicious scripts.
- Malware delivery: Distributing unwanted or harmful code to victims.
- Privilege escalation: Compromising administrative users through persistent scripts.
- Data manipulation or defacement: Changing or disrupting site content.
- Reputation damage: Eroding trust among site users and administrators.
Reference
https://github.com/LabRedesCefetRJ/WeGIA/security/advisories/GHSA-x74c-gwj9-6cwr
Finder
By: CVE-Hunters

