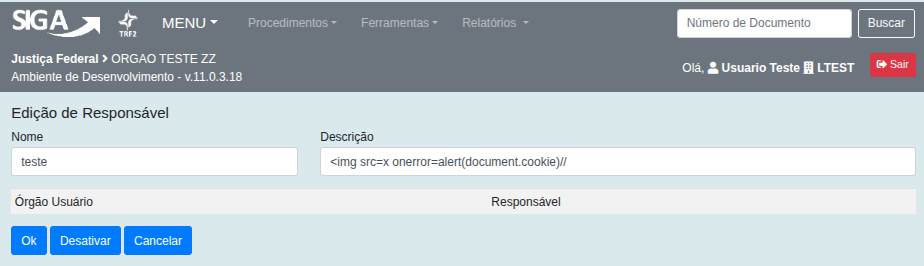
CVE-2026-6990: Cross-Site Scripting (XSS) Stored in new /sigawf/app/responsavel/novo parameter Descrição
CVE Publication: https://www.cve.org/CVERecord?id=CVE-2026-6990
Summary
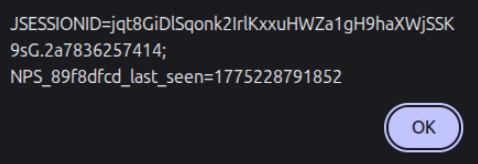
A Stored Cross-Site Scripting (XSS) vulnerability was identified in the /sigawf/app/responsavel/novo endpoint of the SIGA application. This vulnerability allows attackers to inject malicious scripts into the Descrição parameter. The injected scripts are stored on the server and executed automatically whenever the /sigawf/app/responsavel/listar page is accessed by users, representing a significant security risk.
Details
Vulnerable Endpoint: /sigawf/app/responsavel/novo
Parameter: Descrição
PoC
Payload
|
|
Steps to Reproduce:
Register the payload in the Descrição field at the /sigawf/app/responsavel/novo endpoint.
After that, the XSS can be triggered by opening the /sigawf/app/responsavel/listar endpoint.
Impact
- Session hijacking: Stealing cookies or authentication tokens to impersonate users.
- Credential theft: Harvesting usernames and passwords using malicious scripts.
- Malware delivery: Distributing unwanted or harmful code to victims.
- Privilege escalation: Compromising administrative users through persistent scripts.
- Data manipulation or defacement: Changing or disrupting site content.
- Reputation damage: Eroding trust among site users and administrators.
Reference
https://github.com/ViniCastro2001/Security_Reports/tree/main/siga/Stored-XSS-Responsavel
Finder
By: CVE-Hunters

